Updated on March 20, 2026, by OpenEDR
Have you ever held a door open for someone at the office without thinking twice? It seems polite—but in cybersecurity, that simple act could lead to a serious breach. So, what is tailgating in cyber security and why is it such a big concern?
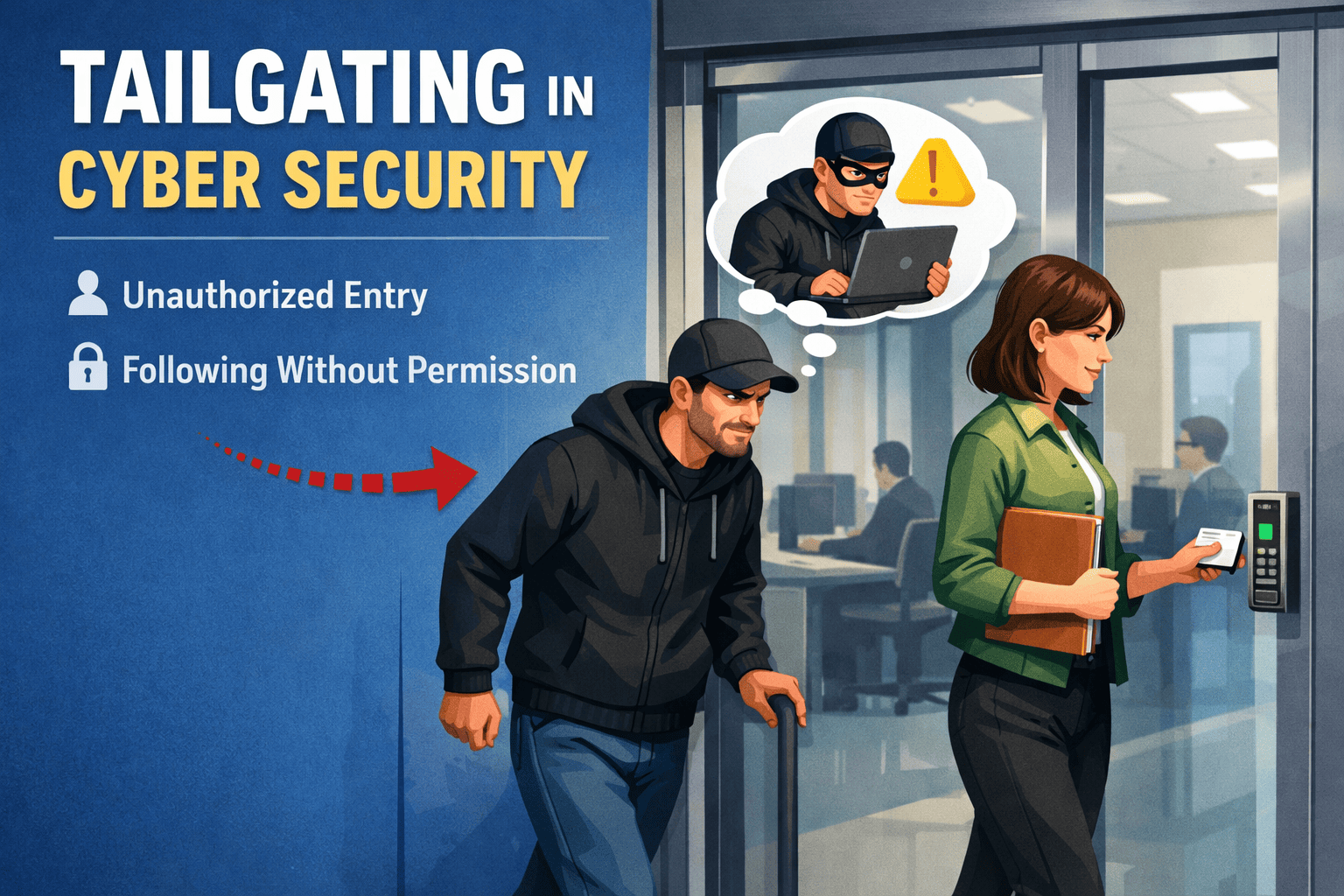
Tailgating, also known as piggybacking, is a physical security breach where an unauthorized person gains access to a restricted area by following someone with legitimate access. While cybersecurity often focuses on digital threats, physical access remains a critical vulnerability.
Understanding what is tailgating in cyber security is essential for IT managers, security professionals, and business leaders. In this guide, we’ll explore how tailgating works, why it’s dangerous, real-world examples, and practical strategies to prevent it.
What is Tailgating in Cyber Security?
Tailgating in cyber security refers to a social engineering attack where an unauthorized individual enters a secure area by exploiting human behavior.
Instead of hacking systems directly, attackers exploit trust and courtesy.
Key Characteristics of Tailgating
Involves physical access to secure areas
Exploits human behavior rather than technology
Often appears harmless or accidental
Can lead to serious security breaches
Understanding what is tailgating in cyber security highlights the importance of combining physical and digital security.
How Tailgating Attacks Work
Tailgating attacks are simple but highly effective.
Step-by-Step Example
An attacker waits near a secure entrance
An authorized employee unlocks the door
The attacker follows closely behind
The employee allows entry out of courtesy
The attacker gains unauthorized access
This method bypasses traditional access controls.
Common Tailgating Tactics
Attackers may use various strategies:
Pretending to be a new employee
Carrying boxes to appear busy
Claiming they forgot their access card
Wearing uniforms or badges
These tactics make the attack seem legitimate.
Why Tailgating is a Serious Security Risk
Tailgating may seem minor, but it can have severe consequences.
Risks of Tailgating Attacks
Unauthorized access to sensitive areas
Theft of data or equipment
Installation of malicious devices
Network compromise
Insider-like access for attackers
Understanding what is tailgating in cyber security helps organizations recognize these risks.
Real-World Examples of Tailgating
Tailgating attacks occur across industries.
Corporate Office Scenario
An attacker follows an employee into an office building and accesses confidential data.
Data Center Breach
Unauthorized individuals enter server rooms and install malicious hardware.
Healthcare Facility Incident
An attacker gains access to patient records by entering restricted areas.
These examples show how tailgating can lead to major breaches.
Tailgating vs Other Social Engineering Attacks
Tailgating is often confused with other social engineering tactics.
Tailgating vs Piggybacking
Tailgating: Unauthorized access without permission
Piggybacking: Access granted knowingly
Tailgating vs Phishing
Tailgating: Physical access attack
Phishing: Digital deception via emails
Tailgating vs Shoulder Surfing
Tailgating: Entering secure areas
Shoulder surfing: Observing sensitive information
Understanding these differences clarifies what is tailgating in cyber security.
Common Targets of Tailgating Attacks
Certain environments are more vulnerable.
High-Risk Locations
Office buildings
Data centers
Hospitals
Financial institutions
Government facilities
Why These Targets?
They contain:
Sensitive data
Critical systems
Valuable equipment
These assets make them attractive targets.
Signs of a Tailgating Attempt
Employees should be aware of warning signs.
Red Flags to Watch For
Someone asking to “borrow” access
Individuals without visible ID badges
People closely following through secure doors
Unfamiliar individuals in restricted areas
Suspicious behavior near entry points
Recognizing these signs helps prevent incidents.
How to Prevent Tailgating Attacks
Organizations must implement strong preventive measures.
1. Enforce Access Control Policies
Strict policies reduce unauthorized access.
Best Practices
Require individual authentication
Prohibit sharing access credentials
Enforce badge usage
2. Use Physical Security Systems
Technology can help prevent tailgating.
Security Tools
Keycard access systems
Biometric authentication
Turnstiles and access gates
Security cameras
3. Train Employees
Employee awareness is critical.
Training Topics
What is tailgating in cyber security
How to identify suspicious behavior
Proper access control practices
Reporting incidents
4. Implement Visitor Management
Track and monitor visitors.
Visitor Controls
Issue temporary badges
Require sign-in procedures
Escort visitors at all times
5. Promote a Security-First Culture
Encourage employees to prioritize security over convenience.
6. Conduct Regular Security Audits
Identify vulnerabilities and improve controls.
Challenges in Preventing Tailgating
Organizations face several challenges.
Human Behavior
People naturally want to be helpful.
Lack of Awareness
Employees may not recognize risks.
Insufficient Security Measures
Weak physical controls increase vulnerability.
Balancing Security and Convenience
Strict controls may impact user experience.
Tailgating in Remote and Hybrid Work Environments
Even in remote settings, tailgating risks exist.
Examples
Unauthorized access to shared workspaces
Weak office security in hybrid environments
Shared credentials in remote teams
Organizations must adapt security strategies accordingly.
The Role of Zero Trust in Preventing Tailgating
Zero trust security assumes no user or device is trusted.
How It Helps
Requires continuous verification
Limits access based on identity
Reduces reliance on physical access alone
Zero trust strengthens defenses against tailgating.
Future Trends in Physical Security
Security is evolving with new technologies.
Emerging Solutions
AI-powered surveillance
Smart access control systems
Behavioral analytics
Integrated physical and digital security
These advancements will help address what is tailgating in cyber security more effectively.
Frequently Asked Questions (FAQ)
What is tailgating in cyber security?
Tailgating is a physical security breach where an unauthorized person gains access to a restricted area by following someone with legitimate access.
Why is tailgating dangerous?
It allows attackers to bypass security controls and access sensitive systems or data.
How can organizations prevent tailgating?
By implementing access controls, employee training, and physical security measures.
What is the difference between tailgating and piggybacking?
Tailgating involves unauthorized access without permission, while piggybacking involves consent.
Is tailgating a cyber or physical threat?
It is primarily a physical security threat but can lead to cyberattacks.
Strengthen Your Security Awareness Today
Understanding what is tailgating in cyber security is crucial for protecting your organization from physical and digital threats. Even the most advanced cybersecurity systems can fail if physical access is compromised.
By combining strong policies, employee training, and modern security tools, organizations can reduce the risk of tailgating attacks.
👉 Register for cybersecurity training today:
https://openedr.platform.xcitium.com/register/
Learn how to identify threats, improve security awareness, and build stronger defenses against evolving cyber risks.