Updated on April 7, 2023, by OpenEDR
How does XDR Explained offer unified and integrated data visibility?
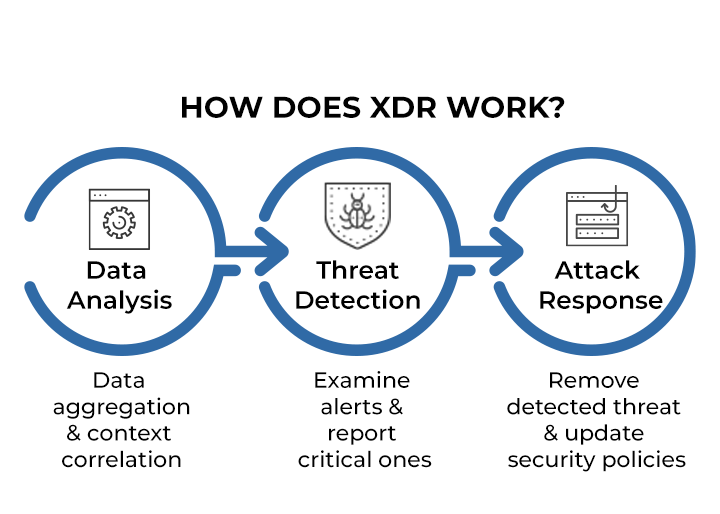
XDR technology provides organizations with a complete threat detection, investigation, and response solution. This technology works by offering unified and integrated data visibility across all networks, endpoints, and cloud resources. Other traditional security systems, like SIEM, EDR, etc., operate in silos offering limited visibility into the cyber threats. These are layered approaches for any security platform. However, XDR takes a different approach to address such limitations. As XDR explained, it unifies data across all security layers to detect threats across the whole attack surface.
Organizations can proactively protect themselves from low-quality security alerts and missing ongoing attacks due to information buried under a massive number of false positive alerts using XDR. The XDR explained organizations’ security teams could see data collected by their security solutions from all platforms within a single dashboard. When you integrate XDR into your security system, your threat analysts can gain insights into threats by combining event data from numerous solutions into a unique contextualized incident.
The Requirements for XDR Explained – What is XDR Security?
The modern security landscape requires XDR technology integration into the organization’s network system. It is required to have a thorough knowledge of the organization’s security environment. As XDR explained, it offers the ability to integrate with modern tools and can detect and respond to threats instantly. Your reliable vendor should offer an XDR solution to give precise threat intelligence and analysis. It should come with flexible deployment options and regulatory compliance.
XDR technology enables a security team to efficiently protect a company against cyberattacks by consolidating security into a single dashboard. Furthermore, XDR makes use of automation to streamline analyst workflows and lessen analyst work without repetitive tasks.
What are the XDR Explained capabilities?
Unlike traditional security solutions, XDR technology consolidates data from multiple security tools into a single platform, providing a holistic view of an organization’s security posture. Here are some of its capabilities:
- Collection of data on a centralized platform
The goal of XDR solutions is to offer centralized security visibility across an organization’s network. Provide the necessary visibility and context; this involves gathering security data from a variety of sources. As XDR explained, it gathers security data from various sources to provide necessary visibility and context. This centralization helps organizations to correlate data from various sources and detect threats that may have gone unnoticed. Analysts can investigate and respond to potential threats more efficiently.
- Accurate data analytics
XDR technology uses advanced analytics and machine learning algorithms to analyze data collected from different security tools. This allows organizations to identify and prioritize security incidents based on their severity and potential impact on the organization.
- Automated response
This advanced technology enables organizations to automate their response to any security events. XDR takes action on an incident on a severity priority basis by blocking access to a specific endpoint or isolating compromised systems to prevent the threat from spreading.
Benefits of XDR Explained
- Single interface management
Your vendor should get your XDR explained as providing a single interface for managing security incidents across the entire enterprise network to configure security settings accordingly.
- Integrated visibility
XDR provides integrated visibility into an organization’s security posture. Security teams can benefit from unified incident response capabilities across all enterprise network environments in the organization. The analysts can improve their overall attack understanding due to unified threat hunting.
- Rapid time to value
XDR technology enables organizations to quickly detect and respond to security incidents. This helps to reduce the time and resources required to investigate and remediate security incidents. This full integration cybersecurity platform with analyst support helps with improving productivity.
The limited security teams within an organization can’t keep up with the growing cybersecurity threat landscape with the traditional layered security approaches. This leads analysts to miss out on important information as they don’t know where to look, no matter how effective the principle is.
Get on with more proactive action in threat detection with the Open EDR solution. It’s a free, sophisticated, open-source EDR solution offering analytic detection with Mitre ATT&CK. Your security team can now see visible event correlation and root cause analysis of adversarial threat activity and behaviors in real-time.
XDR Explained Conclusion: What is XDR in Cyber Security
XDR technology can meet all the requirements for modern cybersecurity threats as it offers a holistic approach to threat detection and response. To provide a unified view of security events, you can integrate XDR technology with existing security tools, such as firewalls, intrusion detection systems, and anti-virus software. Take advantage of its advanced analytics and machine learning capabilities, which can help detect and prevent cyber attacks in real-time.
FAQ Section