Updated on May 6, 2026, by OpenEDR
What happens when hackers gain access to sensitive business data? The answer often begins with a security breach. Today, cyberattacks are growing faster and becoming more sophisticated. Businesses of every size—from startups to global enterprises—face serious risks from data breaches, ransomware, and insider threats.
Understanding the security breach meaning is no longer optional. Whether you are an IT manager, CEO, or cybersecurity professional, knowing how security breaches occur and how to prevent them can protect your organization from financial losses and reputational damage.
In this guide, we’ll explain the security breach meaning, explore common causes, review real-world examples, and share actionable ways to improve cybersecurity defenses.
What Is the Meaning of a Security Breach?
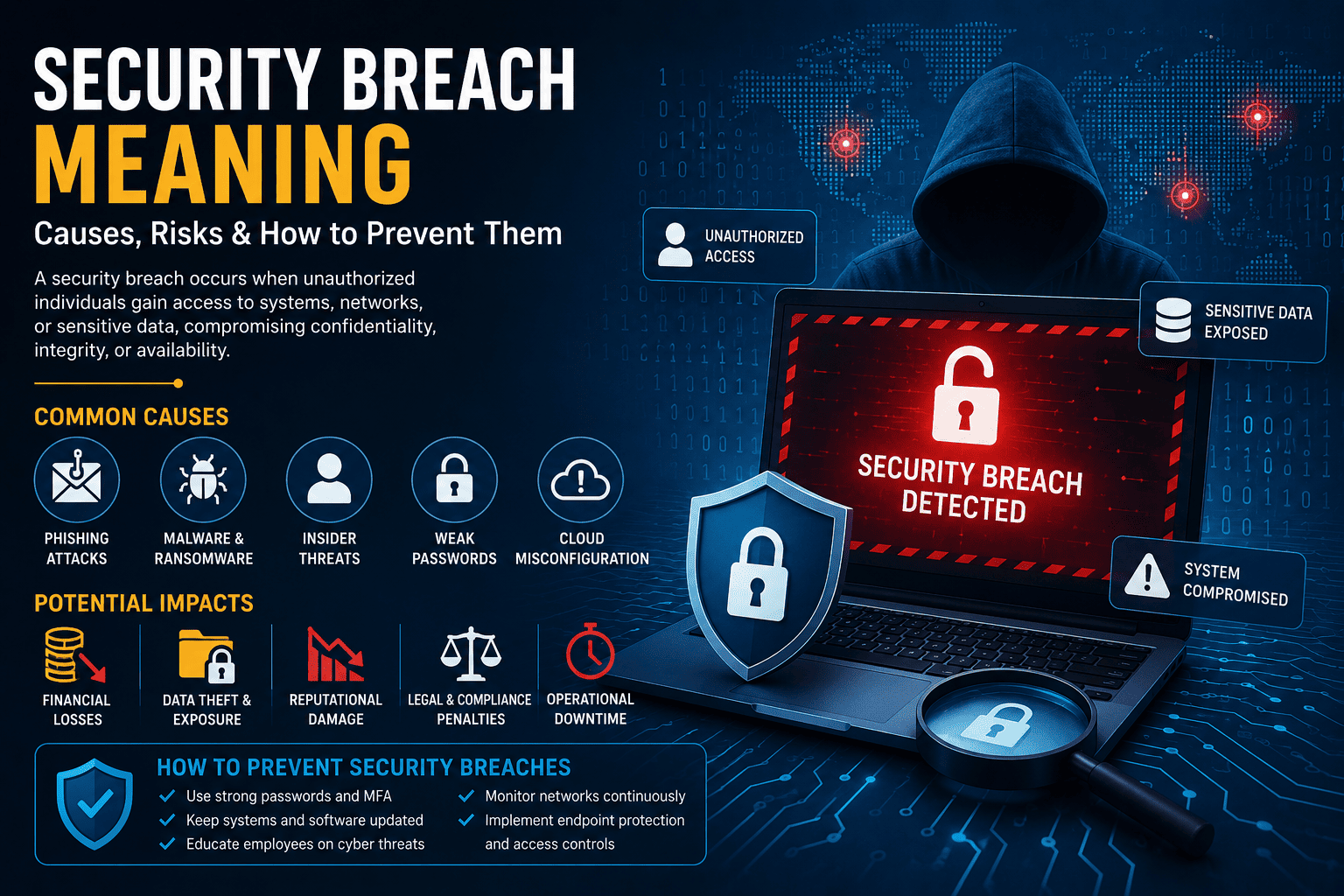
The security breach meaning refers to any incident where unauthorized individuals gain access to systems, networks, applications, or sensitive data. A security breach can expose confidential information, disrupt operations, or allow cybercriminals to steal valuable assets.
A security breach may involve:
- Unauthorized access to systems
- Theft of sensitive data
- Malware or ransomware attacks
- Insider threats
- Weak passwords or poor security practices
In simple terms, a security breach happens when security defenses fail and attackers enter protected environments.
Why Understanding Security Breach Meaning Matters
Many organizations underestimate cyber risks until an attack occurs. However, understanding the security breach meaning helps businesses prepare for threats before damage happens.
Key reasons it matters:
- Protects sensitive customer data
- Reduces financial losses
- Prevents operational downtime
- Helps meet compliance requirements
- Builds customer trust
For modern businesses, cybersecurity is not just an IT issue—it’s a business survival strategy.
Common Types of Security Breaches
Security breaches come in many forms. Understanding the different types helps organizations strengthen defenses.
1. Data Breaches
A data breach occurs when confidential information is exposed or stolen.
Examples:
- Customer records
- Credit card information
- Login credentials
- Medical records
Data breaches often lead to identity theft and financial fraud.
2. Malware Attacks
Malware is malicious software designed to damage systems or steal data.
Common malware types:
- Ransomware
- Trojans
- Spyware
- Worms
These attacks can spread quickly across networks.
3. Phishing Attacks
Phishing tricks users into revealing sensitive information through fake emails or websites.
Attackers often target:
- Employees
- Executives
- Finance teams
Phishing remains one of the leading causes of security breaches.
4. Insider Threats
Not all breaches come from external hackers. Employees or contractors can intentionally or accidentally expose data.
Insider risks include:
- Weak passwords
- Human error
- Unauthorized file sharing
Even trusted users can create vulnerabilities.
5. Cloud Security Breaches
As businesses move to cloud environments, cloud misconfigurations have become a major risk.
Common cloud vulnerabilities:
- Publicly exposed databases
- Weak access controls
- Poor API security
Cloud security must be continuously monitored.
Major Causes of Security Breaches
To fully understand the security breach meaning, it’s important to know what causes these incidents.
Weak Passwords
Simple or reused passwords make it easy for attackers to gain access.
Best practices:
- Use strong passwords
- Enable multi-factor authentication (MFA)
- Avoid password reuse
Unpatched Software
Outdated systems often contain known vulnerabilities.
Cybercriminals actively scan for:
- Old applications
- Unpatched operating systems
- Unsupported software
Regular updates reduce risks significantly.
Human Error
Employees remain one of the weakest links in cybersecurity.
Common mistakes:
- Clicking malicious links
- Sharing sensitive data
- Misconfiguring systems
Security awareness training is critical.
Lack of Network Monitoring
Without visibility into network activity, organizations may not detect attacks early.
Continuous monitoring helps:
- Identify suspicious behavior
- Detect intrusions quickly
- Reduce response time
Signs Your Organization May Have Experienced a Security Breach
Recognizing warning signs early can minimize damage.
Common indicators include:
- Unusual login activity
- Slow system performance
- Missing or altered files
- Unexpected software installations
- Suspicious outbound traffic
If these signs appear, immediate investigation is necessary.
Real-World Security Breach Examples
Real incidents highlight the importance of understanding the security breach meaning.
Retail Data Breach
A large retailer suffered a breach after attackers stole employee credentials. Millions of customer payment records were exposed.
Lessons learned:
- Strengthen authentication
- Monitor third-party access
- Use network segmentation
Ransomware Attack on Healthcare
A hospital network experienced ransomware that encrypted patient data.
Impact:
- Delayed medical services
- Financial losses
- Compliance penalties
Healthcare organizations are major targets because of sensitive data.
Cloud Misconfiguration Incident
A company accidentally exposed customer information through an unsecured cloud database.
Key takeaway:
Cloud security requires proper configuration and continuous monitoring.
The Financial Impact of Security Breaches
Security breaches can cost businesses millions.
Common financial consequences:
- Legal penalties
- Regulatory fines
- Downtime costs
- Incident response expenses
- Reputation damage
For small businesses, even a single breach can threaten survival.
How to Prevent Security Breaches
Preventing cyberattacks requires a proactive strategy.
1. Implement Multi-Factor Authentication
MFA adds an extra layer of protection beyond passwords.
Benefits:
- Reduces credential theft risks
- Prevents unauthorized access
2. Use Endpoint Detection and Response (EDR)
EDR solutions monitor endpoints for suspicious behavior.
Capabilities include:
- Threat detection
- Automated response
- Malware isolation
Modern EDR tools improve breach prevention.
3. Conduct Employee Training
Employees must recognize phishing and social engineering tactics.
Training should cover:
- Email security
- Password management
- Safe browsing habits
Security awareness reduces human error.
4. Monitor Networks Continuously
Continuous network monitoring helps organizations detect threats early.
Benefits:
- Real-time visibility
- Faster incident response
- Better threat intelligence
Monitoring is essential for modern cybersecurity.
5. Keep Systems Updated
Patch vulnerabilities before attackers exploit them.
Update regularly:
- Operating systems
- Applications
- Security tools
A strong patch management process is critical.
Security Breach vs Data Breach: What’s the Difference?
Many people confuse these terms.
| Security Breach | Data Breach |
|---|---|
| Unauthorized access to systems | Exposure or theft of data |
| Broader cybersecurity incident | Specific type of breach |
| May not involve stolen data | Always involves compromised data |
A data breach is a type of security breach, but not all security breaches result in data theft.
How Businesses Should Respond to a Security Breach
Fast action reduces damage.
Incident Response Steps
1. Contain the Threat
Disconnect affected systems immediately.
2. Investigate the Incident
Determine how attackers gained access.
3. Notify Stakeholders
Inform customers, partners, and regulators if necessary.
4. Recover Systems
Restore operations securely.
5. Strengthen Security
Fix vulnerabilities to prevent future attacks.
An incident response plan is essential for every organization.
Future Trends in Security Breach Prevention
Cybersecurity continues evolving rapidly.
Emerging trends include:
- AI-powered threat detection
- Zero Trust security models
- Behavioral analytics
- Cloud-native security solutions
- Automated response systems
Businesses that adopt advanced security strategies will stay ahead of attackers.
Why CEOs and IT Leaders Must Prioritize Cybersecurity
Cybersecurity is no longer only the IT department’s responsibility.
Executives must:
- Invest in security tools
- Support employee training
- Build incident response plans
- Encourage a security-first culture
Understanding the security breach meaning helps leaders make smarter business decisions.
Conclusion
Cyber threats are increasing every year, and businesses cannot afford to ignore them. Understanding the security breach meaning is the first step toward building stronger cybersecurity defenses.
From phishing attacks to ransomware and insider threats, security breaches can cause serious financial and operational damage. However, with proactive monitoring, employee training, and modern security tools, organizations can reduce risks significantly.
Strong cybersecurity protects not just systems and data—but also business reputation and customer trust.
Protect Your Business Before a Security Breach Happens
Don’t wait until attackers compromise your systems. Strengthen your cybersecurity defenses today with advanced endpoint detection and threat monitoring.
👉 Get started now: https://openedr.platform.xcitium.com/register/
FAQs
1. What is the meaning of a security breach?
A security breach is an incident where unauthorized individuals gain access to systems, networks, or sensitive data.
2. What causes security breaches?
Common causes include phishing attacks, weak passwords, malware, insider threats, and unpatched software.
3. What is the difference between a security breach and a data breach?
A security breach is broader and may involve unauthorized system access, while a data breach specifically refers to stolen or exposed information.
4. How can businesses prevent security breaches?
Businesses can prevent breaches by using MFA, endpoint protection, employee training, and continuous network monitoring.
5. Why are security breaches dangerous?
Security breaches can lead to financial losses, reputational damage, operational downtime, and legal penalties.