Updated on February 11, 2026, by OpenEDR
Cyberattacks rarely start with firewalls. Instead, they begin with stolen credentials, weak passwords, or compromised accounts. In fact, most data breaches today involve identity misuse. That’s why organizations are rapidly investing in identity access management solutions to secure users, systems, and sensitive data.
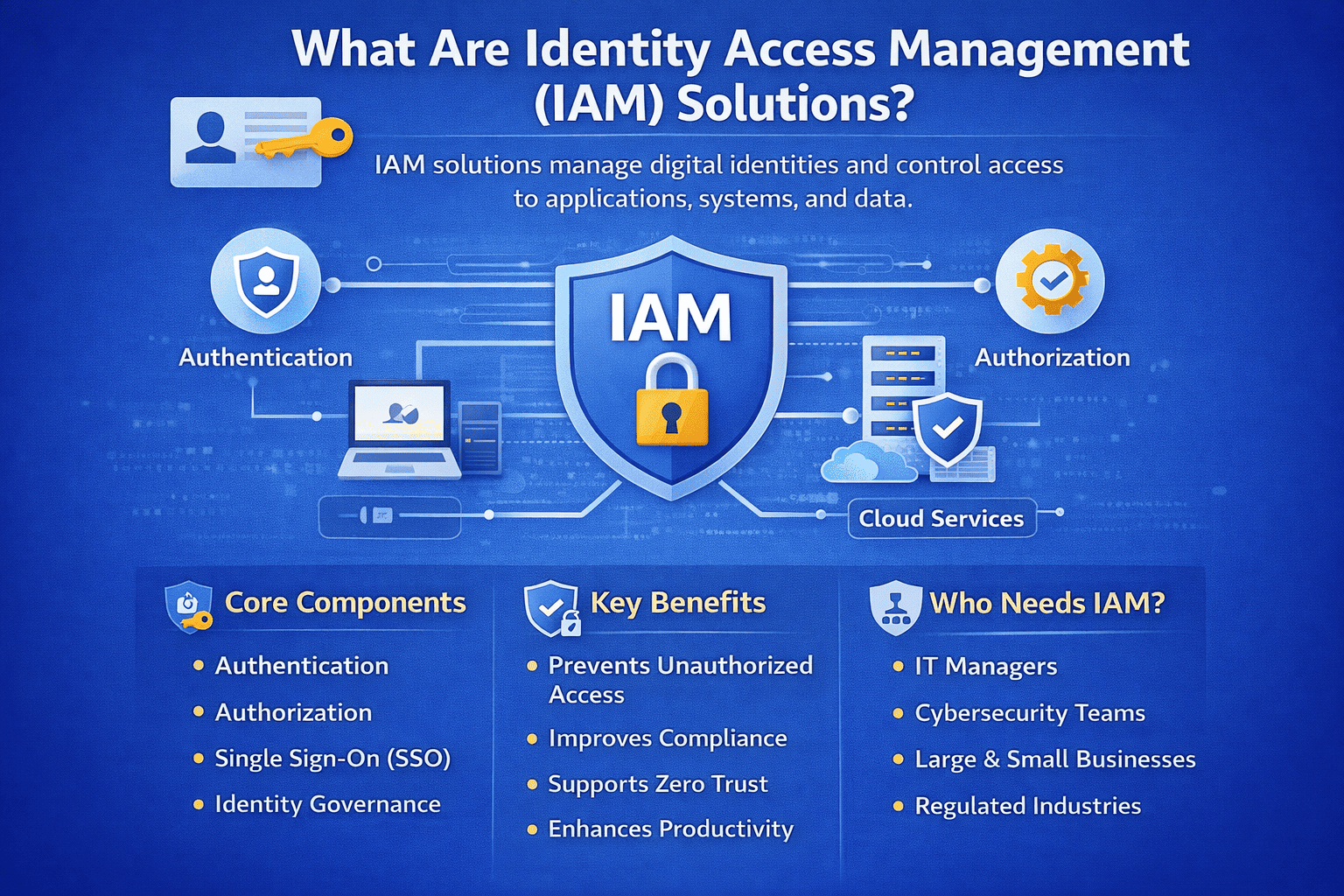
Identity access management solutions control who can access what, when, and under what conditions. They help businesses enforce policies, reduce insider threats, and support Zero Trust security models. For IT managers and cybersecurity leaders, these solutions are no longer optional—they are foundational.
In this guide, we’ll explore what identity access management solutions are, how they work, key components, benefits, use cases, and how to choose the right approach for your organization.
What Are Identity Access Management Solutions?
Identity access management solutions (IAM solutions) are security systems that manage digital identities and control access to applications, networks, and data.
At a high level, identity access management solutions ensure:
The right user gets the right access
Access is granted at the right time
Access follows security policies
Unauthorized users are blocked
IAM bridges identity verification and access control in a structured, secure way.
Why Identity Access Management Solutions Matter Today
Digital transformation has increased access complexity.
Employees now use:
Cloud platforms
SaaS applications
Remote devices
Hybrid infrastructures
APIs and microservices
Without identity access management solutions, organizations risk uncontrolled access sprawl.
Key business drivers for IAM:
Remote and hybrid work
Cloud adoption
Regulatory compliance
Rising insider threats
Credential-based attacks
Strong identity governance reduces enterprise risk.
Core Components of Identity Access Management Solutions
Modern identity access management solutions consist of several integrated components.
1. Authentication
Authentication verifies user identity.
Common authentication methods include:
Password-based login
Multi-Factor Authentication (MFA)
Biometric authentication
Hardware tokens
Strong authentication reduces credential misuse.
2. Authorization
Authorization determines what a user can access.
It includes:
Role-Based Access Control (RBAC)
Attribute-Based Access Control (ABAC)
Least privilege enforcement
Authorization ensures users access only what they need.
3. Identity Governance
Identity governance manages identity lifecycle processes.
It includes:
User provisioning
Deprovisioning
Access reviews
Role audits
Governance reduces dormant account risk.
4. Single Sign-On (SSO)
SSO allows users to access multiple applications with one login.
Benefits include:
Improved user experience
Reduced password fatigue
Fewer helpdesk requests
SSO strengthens both security and productivity.
5. Privileged Access Management (PAM)
Privileged accounts are high-risk.
Identity access management solutions often integrate with PAM to:
Monitor admin access
Record privileged sessions
Enforce time-limited permissions
Detect abnormal behavior
Privileged account protection is critical for breach prevention.
How Identity Access Management Solutions Work
Identity access management solutions operate through structured workflows.
Typical process:
A user requests access
Identity is verified
Access rights are assigned
Policies enforce conditions
Activity is monitored
Access is revoked when no longer needed
Automation improves speed and consistency.
Identity Access Management Solutions and Zero Trust
Zero Trust is based on “never trust, always verify.”
Identity access management solutions enable Zero Trust by:
Enforcing continuous authentication
Validating device posture
Monitoring session risk
Blocking suspicious activity
IAM is a core pillar of Zero Trust architecture.
Benefits of Identity Access Management Solutions
Organizations adopting identity access management solutions experience measurable benefits.
Key advantages include:
Reduced breach risk
Improved compliance posture
Enhanced user productivity
Centralized access control
Faster onboarding and offboarding
For executives, IAM reduces operational and reputational risk.
Identity Access Management Solutions in Cloud Environments
Cloud adoption increases identity complexity.
Identity access management solutions support:
SaaS application control
Cloud infrastructure access
API authentication
Federated identity management
They provide centralized visibility across hybrid environments.
IAM and Regulatory Compliance
Regulatory standards increasingly demand strict identity controls.
Identity access management solutions support compliance frameworks such as:
HIPAA
GDPR
PCI DSS
SOX
ISO 27001
Audit logs and automated reviews simplify compliance reporting.
Common Identity-Based Threats
Understanding identity threats highlights the importance of IAM.
Common risks include:
Phishing attacks
Credential stuffing
Insider misuse
Privilege escalation
Account takeover
Identity access management solutions help detect and prevent these threats.
Identity Lifecycle Management
Identity lifecycle management is a key function of IAM.
It includes:
Employee onboarding
Role changes
Access modifications
Termination deactivation
Automated lifecycle processes reduce security gaps.
Identity Access Management Solutions for Different Industries
Different sectors have unique identity challenges.
Healthcare
Protect patient records and meet strict privacy regulations.
Financial Services
Prevent fraud and secure sensitive financial data.
Retail and E-Commerce
Secure customer accounts and payment systems.
Technology and SaaS
Protect intellectual property and development environments.
Government
Enforce strict identity validation and access control policies.
IAM adapts to industry-specific security requirements.
Cloud vs On-Premises IAM
Organizations may choose:
Cloud-based identity access management solutions
On-premises IAM deployments
Hybrid identity frameworks
Cloud IAM offers scalability and easier updates. On-premises solutions offer direct control. Hybrid models balance flexibility and oversight.
Common IAM Implementation Challenges
While powerful, identity access management solutions require careful deployment.
Common challenges:
Legacy system integration
Role complexity
User resistance
Policy misconfiguration
Over-permissioned accounts
Planning and phased rollout reduce friction.
Best Practices for Deploying Identity Access Management Solutions
To maximize effectiveness:
Implement MFA everywhere
Enforce least privilege
Conduct regular access reviews
Monitor privileged accounts
Integrate with SIEM and endpoint tools
Automate identity lifecycle workflows
These steps strengthen IAM maturity.
Identity Access Management Solutions vs Traditional Access Control
Traditional access control was perimeter-based.
Modern identity access management solutions are identity-centric.
They:
Focus on users, not networks
Protect cloud and remote access
Enable dynamic policy enforcement
Monitor real-time behavior
Identity is now the new perimeter.
The Future of Identity Access Management Solutions
IAM continues evolving.
Emerging trends include:
Passwordless authentication
Behavioral biometrics
AI-driven risk scoring
Adaptive access controls
Integration with Extended Detection and Response (XDR)
Identity security is becoming more intelligent and automated.
Measuring IAM Effectiveness
Organizations should track IAM performance metrics.
Key metrics:
Failed login attempts
Privileged access incidents
Dormant account reduction
Access request turnaround time
Audit findings
Continuous measurement improves outcomes.
FAQs: Identity Access Management Solutions
1. What are identity access management solutions?
They are systems that manage user identities and control access to applications, systems, and data.
2. Why are identity access management solutions important?
They prevent unauthorized access and reduce identity-based attacks.
3. Do identity access management solutions replace firewalls?
No. They complement network and endpoint security tools.
4. What is the difference between IAM and PAM?
IAM manages general access. PAM focuses on privileged accounts.
5. Are identity access management solutions suitable for small businesses?
Yes. Even small organizations benefit from centralized identity control.
Final Thoughts: Why Identity Access Management Solutions Are Essential
Identity has become the primary attack surface in modern enterprises. As organizations expand into cloud environments and remote work models, managing access grows more complex. Identity access management solutions provide the structure, visibility, and enforcement needed to protect users and data.
For IT managers, IAM reduces operational risk.
For cybersecurity teams, it strengthens threat prevention.
For executives, it protects brand trust and regulatory compliance.
Identity access management solutions are not just technical tools—they are strategic investments in long-term security resilience.
Take the Next Step Toward Stronger Identity Security
Ready to gain deeper visibility into user behavior and strengthen your security posture?
👉 Register today:
https://openedr.platform.xcitium.com/register/
Discover how advanced endpoint and identity-focused security solutions help organizations prevent breaches, detect anomalies, and maintain full control over access across modern environments.