Updated on March 24, 2026, by OpenEDR
How confident are you that your organization’s data is truly secure? In today’s threat landscape, achieving assured information security is no longer a luxury—it’s a necessity.
Cyberattacks are increasing in frequency and sophistication. From ransomware to insider threats, businesses face constant risks. Without a structured approach to assured information security, even well-funded organizations can fall victim to breaches.
In this guide, we’ll explore what assured information security means, why it matters, and how you can implement it effectively to protect your business.
What Is Assured Information Security?
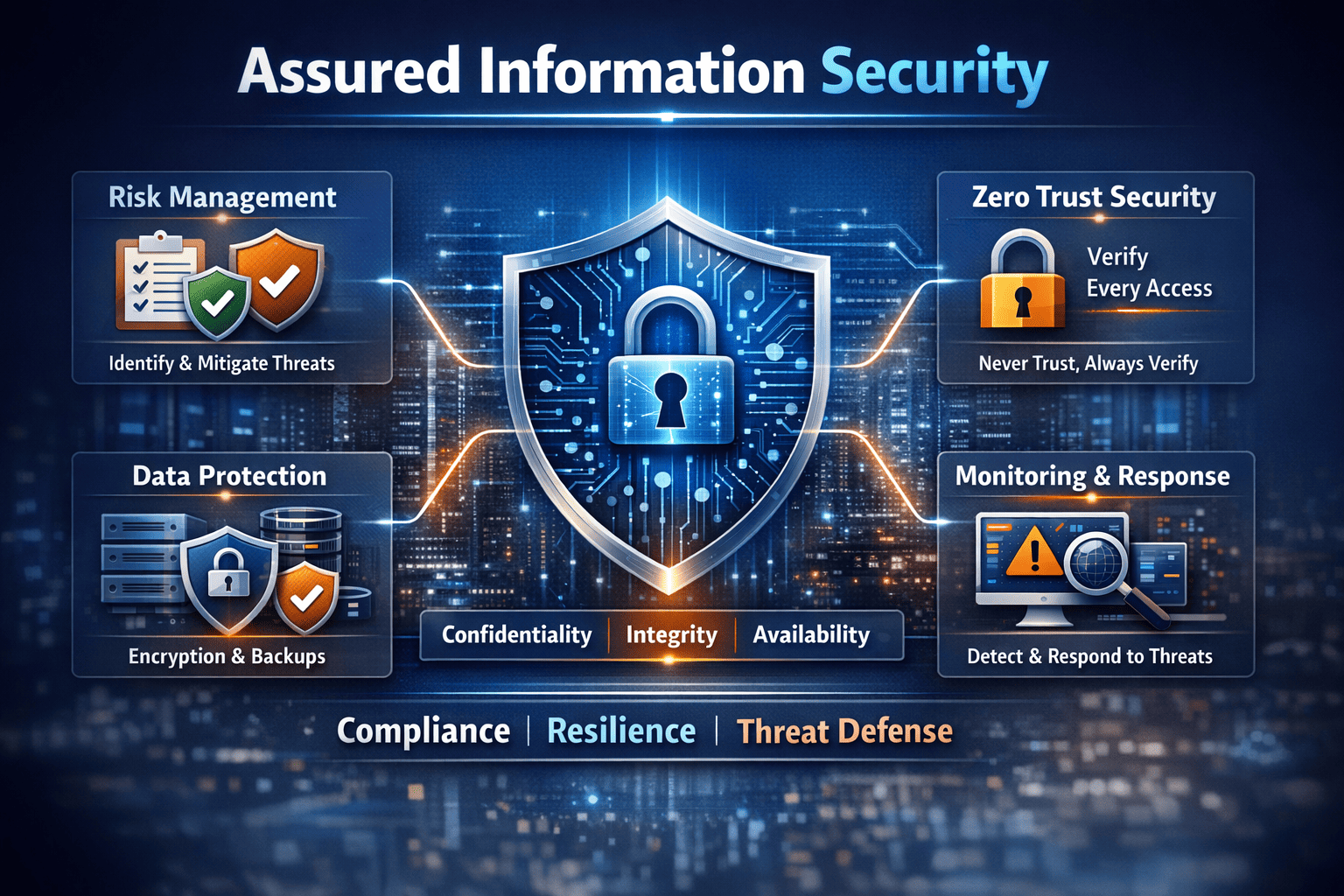
Assured information security refers to a comprehensive approach to protecting data, systems, and networks with guaranteed levels of confidentiality, integrity, and availability.
It goes beyond basic security measures by ensuring:
- Continuous protection against evolving threats
- Verified security controls and processes
- Measurable risk reduction
In simple terms, it’s about having confidence that your security systems actually work when needed.
Why Assured Information Security Is Critical Today
Modern organizations rely heavily on digital systems. This dependency increases the impact of any security failure.
Key Reasons It Matters:
- Rising Cyber Threats: Attackers use advanced techniques like AI-driven malware.
- Regulatory Compliance: Laws like GDPR and HIPAA require strong data protection.
- Remote Work Risks: Distributed workforces expand the attack surface.
- Business Continuity: Security failures can disrupt operations.
Without assured information security, businesses risk financial loss, reputational damage, and legal consequences.
Core Principles of Assured Information Security
To achieve assured information security, organizations must focus on foundational principles.
1. Confidentiality
Ensure that sensitive data is accessible only to authorized users.
2. Integrity
Protect data from unauthorized modification or tampering.
3. Availability
Ensure systems and data are accessible when needed.
These three pillars form the backbone of any effective security strategy.
Key Components of an Assured Information Security Framework
Building assured information security requires multiple layers of protection working together.
1. Risk Assessment and Management
Understanding risks is the first step.
- Identify vulnerabilities
- Evaluate potential threats
- Prioritize risks based on impact
Regular risk assessments help organizations stay ahead of threats.
2. Identity and Access Management (IAM)
Controlling access is critical for assured information security.
Implement:
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Zero Trust access models
This ensures only the right users access sensitive data.
3. Endpoint Security
Endpoints are often the weakest link.
Protect devices with:
- Antivirus and anti-malware tools
- Endpoint Detection and Response (EDR)
- Continuous monitoring
This reduces the risk of breaches from compromised devices.
4. Network Security
A secure network is essential for assured information security.
Use:
- Firewalls
- Intrusion detection systems (IDS)
- Secure VPNs
These tools protect data in transit and prevent unauthorized access.
5. Data Protection and Encryption
Data must be protected at all times.
Best practices include:
- Encrypting data at rest and in transit
- Implementing data loss prevention (DLP)
- Regular backups
This ensures data remains secure even if systems are compromised.
Common Challenges in Achieving Assured Information Security
Despite best efforts, organizations face several challenges.
Complex IT Environments
Hybrid cloud and multi-device ecosystems increase complexity.
Human Error
Employees can unintentionally expose sensitive data.
Evolving Threat Landscape
Cyber threats continuously adapt and evolve.
Limited Visibility
Lack of real-time monitoring reduces response effectiveness.
Addressing these challenges is key to maintaining assured information security.
Best Practices to Achieve Assured Information Security
To build a strong security posture, follow these actionable steps:
Implement a Zero Trust Architecture
Never trust any user or device by default.
Automate Security Processes
Use automation to detect and respond to threats faster.
Conduct Regular Security Audits
Identify gaps and improve controls continuously.
Train Employees
Educate staff on phishing, password hygiene, and safe practices.
Use Advanced Threat Detection
Leverage AI and machine learning for proactive defense.
Role of Compliance and Standards
Compliance frameworks play a vital role in assured information security.
Common Standards:
- ISO 27001
- NIST Cybersecurity Framework
- CIS Controls
These frameworks provide structured guidelines to improve security posture.
How Zero Trust Enhances Assured Information Security
Zero Trust is a modern approach that aligns perfectly with assured information security.
Key Benefits:
- Continuous verification of users and devices
- Reduced attack surface
- Better visibility and control
By adopting Zero Trust, organizations can significantly strengthen their defenses.
Real-World Example
Consider a company that implemented assured information security practices:
- Enforced MFA across all systems
- Used EDR for endpoint protection
- Implemented Zero Trust access
When a phishing attack occurred, the threat was detected and contained instantly—preventing a major breach.
Future Trends in Assured Information Security
The future of assured information security is evolving rapidly.
Emerging Trends:
- AI-driven cybersecurity
- Cloud-native security platforms
- Behavioral analytics
- Automated incident response
Organizations that adopt these technologies will stay ahead of cyber threats.
Conclusion
Assured information security is essential for protecting modern businesses from evolving cyber threats.
By implementing strong controls, adopting Zero Trust, and leveraging advanced technologies, organizations can:
- Reduce risks
- Improve resilience
- Protect sensitive data
Security is no longer just an IT concern—it’s a business priority.
🚀 Strengthen Your Security Today
Take the first step toward achieving assured information security.
👉 Get started now: https://openedr.platform.xcitium.com/register/
FAQs: Assured Information Security
1. What is assured information security?
It is a comprehensive approach to ensuring data confidentiality, integrity, and availability with verified security controls.
2. Why is assured information security important?
It protects businesses from cyber threats, ensures compliance, and supports business continuity.
3. What are the key components of assured information security?
Risk management, IAM, endpoint security, network security, and data protection.
4. How does Zero Trust improve security?
It continuously verifies users and devices, reducing unauthorized access risks.
5. What tools help achieve assured information security?
EDR, SIEM, IAM solutions, and AI-driven security platforms are commonly used.