Updated on April 6, 2026, by OpenEDR
Cyber threats are evolving faster than ever. From ransomware attacks to data breaches, organizations across industries are under constant pressure to strengthen their defenses. This is where the NIST cyber security framework plays a crucial role.
The NIST cyber security framework provides a structured approach to managing cybersecurity risks. Whether you’re an IT manager, security professional, or business leader, understanding this framework can help you build a stronger and more resilient security posture.
In this guide, we’ll break down everything you need to know about the NIST cyber security framework, including its core functions, benefits, and how to implement it effectively.
What is the NIST Cyber Security Framework?
The NIST cyber security framework is a set of guidelines developed by the National Institute of Standards and Technology (NIST) to help organizations manage and reduce cybersecurity risks.
It is widely used across industries because it is:
- Flexible and adaptable
- Risk-based
- Easy to implement
- Scalable for businesses of all sizes
The framework helps organizations identify threats, protect systems, detect incidents, respond effectively, and recover quickly.
Core Functions of the NIST Cyber Security Framework
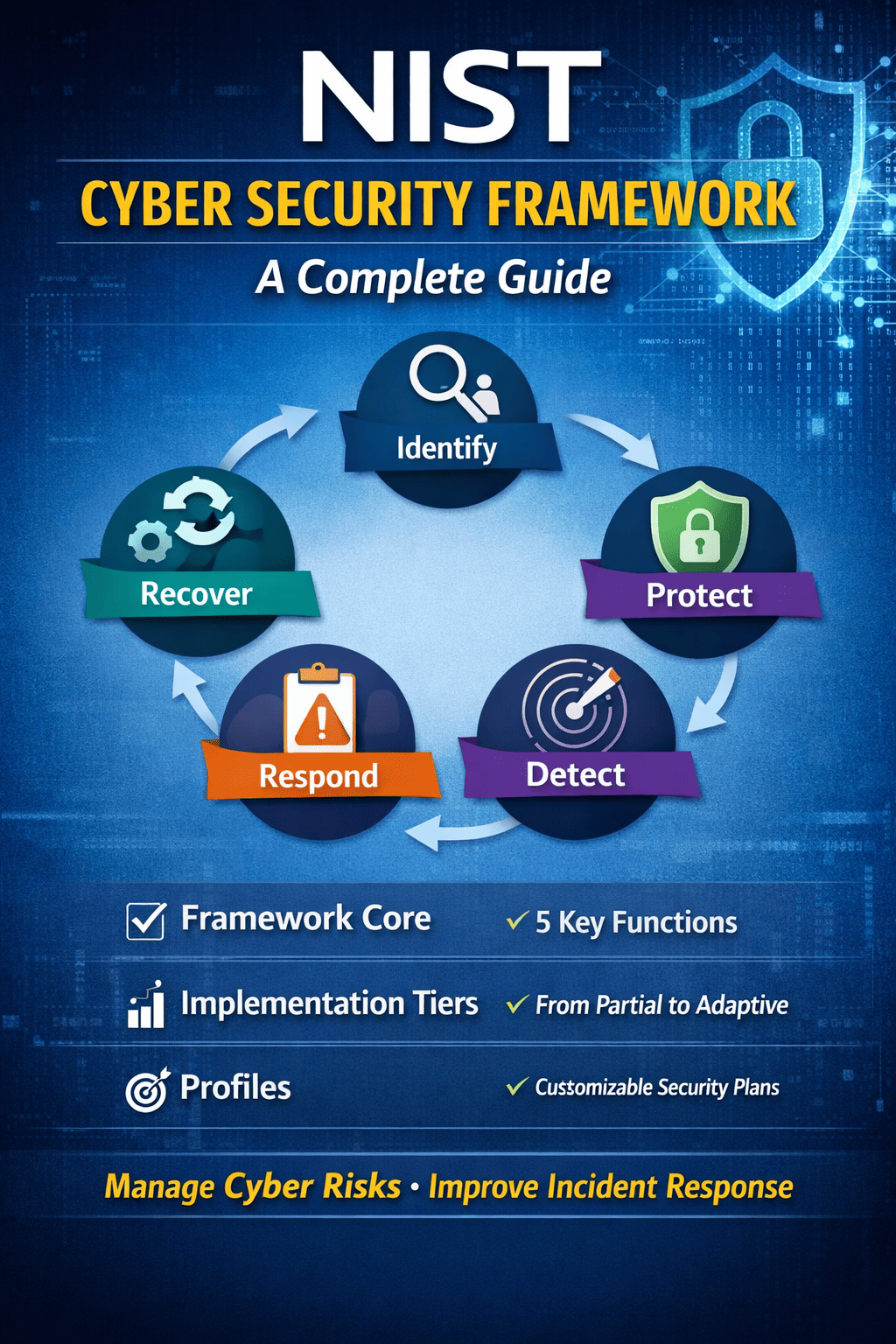
At the heart of the NIST cyber security framework are five core functions. These functions provide a lifecycle approach to cybersecurity.
1. Identify
This function focuses on understanding your organization’s environment, assets, and risks.
Key activities include:
- Asset management
- Risk assessment
- Business environment analysis
- Governance and policies
Understanding what needs protection is the first step in the NIST cyber security framework.
2. Protect
The Protect function ensures safeguards are in place to secure critical assets.
Examples include:
- Access control
- Data security
- Employee training
- Maintenance and protective technologies
This step minimizes the impact of potential cyber incidents.
3. Detect
Detect focuses on identifying cybersecurity events quickly.
Key components:
- Continuous monitoring
- Anomaly detection
- Security event logging
Early detection is essential to reducing damage and response time.
4. Respond
This function outlines how to react to cybersecurity incidents.
It includes:
- Incident response planning
- Communication strategies
- Threat analysis
- Mitigation actions
A strong response plan ensures minimal disruption.
5. Recover
Recover helps organizations restore systems and operations after an attack.
Key elements:
- Recovery planning
- Improvements based on lessons learned
- Communication with stakeholders
This ensures business continuity after an incident.
How the NIST Cyber Security Framework Works
The NIST cyber security framework is built around three main components:
Framework Core
Defines cybersecurity activities and outcomes (the five functions)
Implementation Tiers
Measures how mature your cybersecurity practices are:
- Tier 1: Partial
- Tier 2: Risk-informed
- Tier 3: Repeatable
- Tier 4: Adaptive
Profiles
Align cybersecurity activities with business requirements and risk tolerance
Together, these components help organizations customize the NIST cyber security framework based on their needs.
Benefits of the NIST Cyber Security Framework
Implementing the NIST cyber security framework offers several advantages:
Improved Risk Management
Helps identify and prioritize cybersecurity risks effectively
Better Incident Response
Ensures faster and more structured response to threats
Regulatory Compliance
Aligns with many compliance standards like ISO, HIPAA, and GDPR
Scalable Security
Works for small businesses and large enterprises alike
Enhanced Visibility
Provides a clear view of your organization’s security posture
Who Should Use the NIST Cyber Security Framework?
The NIST cyber security framework is designed for organizations of all sizes and industries.
It is especially useful for:
- IT and security teams
- Financial institutions
- Healthcare organizations
- Government agencies
- SaaS and tech companies
Even startups can benefit by adopting a structured cybersecurity approach early.
How to Implement the NIST Cyber Security Framework
Implementing the NIST cyber security framework doesn’t have to be complicated. Follow these steps:
Step 1: Assess Current Security Posture
Identify existing controls, risks, and vulnerabilities.
Step 2: Define a Target Profile
Determine your desired cybersecurity outcomes.
Step 3: Identify Gaps
Compare current vs target state to find weaknesses.
Step 4: Create an Action Plan
Prioritize improvements based on risk levels.
Step 5: Monitor and Improve
Continuously evaluate and update your strategy.
NIST Cyber Security Framework vs Other Standards
| Feature | NIST Cyber Security Framework | ISO 27001 |
|---|---|---|
| Approach | Risk-based | Compliance-based |
| Flexibility | High | Moderate |
| Implementation Complexity | Moderate | High |
| Cost | Low | Higher |
The NIST cyber security framework is often preferred for its flexibility and ease of adoption.
Common Challenges in Implementation
While the NIST cyber security framework is powerful, organizations may face challenges:
- Lack of cybersecurity expertise
- Limited budget or resources
- Difficulty integrating with existing systems
- Resistance to organizational change
Overcoming these challenges requires proper planning and leadership support.
Best Practices for Success
To get the most out of the NIST cyber security framework, follow these best practices:
- Regularly update risk assessments
- Train employees on cybersecurity awareness
- Use automation tools for monitoring
- Integrate threat intelligence
- Continuously improve processes
Consistency is key to long-term success.
FAQs About NIST Cyber Security Framework
1. What is the main purpose of the NIST cyber security framework?
The main purpose of the NIST cyber security framework is to help organizations identify, manage, and reduce cybersecurity risks using a structured and flexible approach.
2. Is the NIST cyber security framework mandatory?
No, the NIST cyber security framework is not mandatory, but it is widely recommended and used as a best practice across industries.
3. Can small businesses use the NIST cyber security framework?
Yes, the NIST cyber security framework is scalable and can be adapted for small businesses as well as large enterprises.
4. How long does it take to implement the NIST cyber security framework?
Implementation time varies depending on the organization’s size and complexity, but it typically takes several weeks to months.
5. Is the NIST cyber security framework suitable for cloud environments?
Yes, the NIST cyber security framework can be applied to cloud, on-premise, and hybrid environments.
Final Thoughts
The NIST cyber security framework is one of the most effective tools for managing cybersecurity risks in today’s digital landscape. It provides a clear roadmap for identifying threats, protecting systems, and responding to incidents.
For organizations looking to strengthen their cybersecurity posture, adopting the NIST cyber security framework is not just a best practice—it’s a necessity.
Take Action Now
Want to take your cybersecurity to the next level?
👉 Start protecting your endpoints with advanced detection and response:
https://openedr.platform.xcitium.com/register/