Updated on February 11, 2026, by OpenEDR
Cloud adoption has transformed how organizations operate. Employees access SaaS platforms from anywhere, data flows across multiple environments, and hybrid work has become the norm. But with this flexibility comes risk. Sensitive data can be exposed, compliance gaps can widen, and shadow IT can grow unchecked. That’s where CASB security becomes essential.
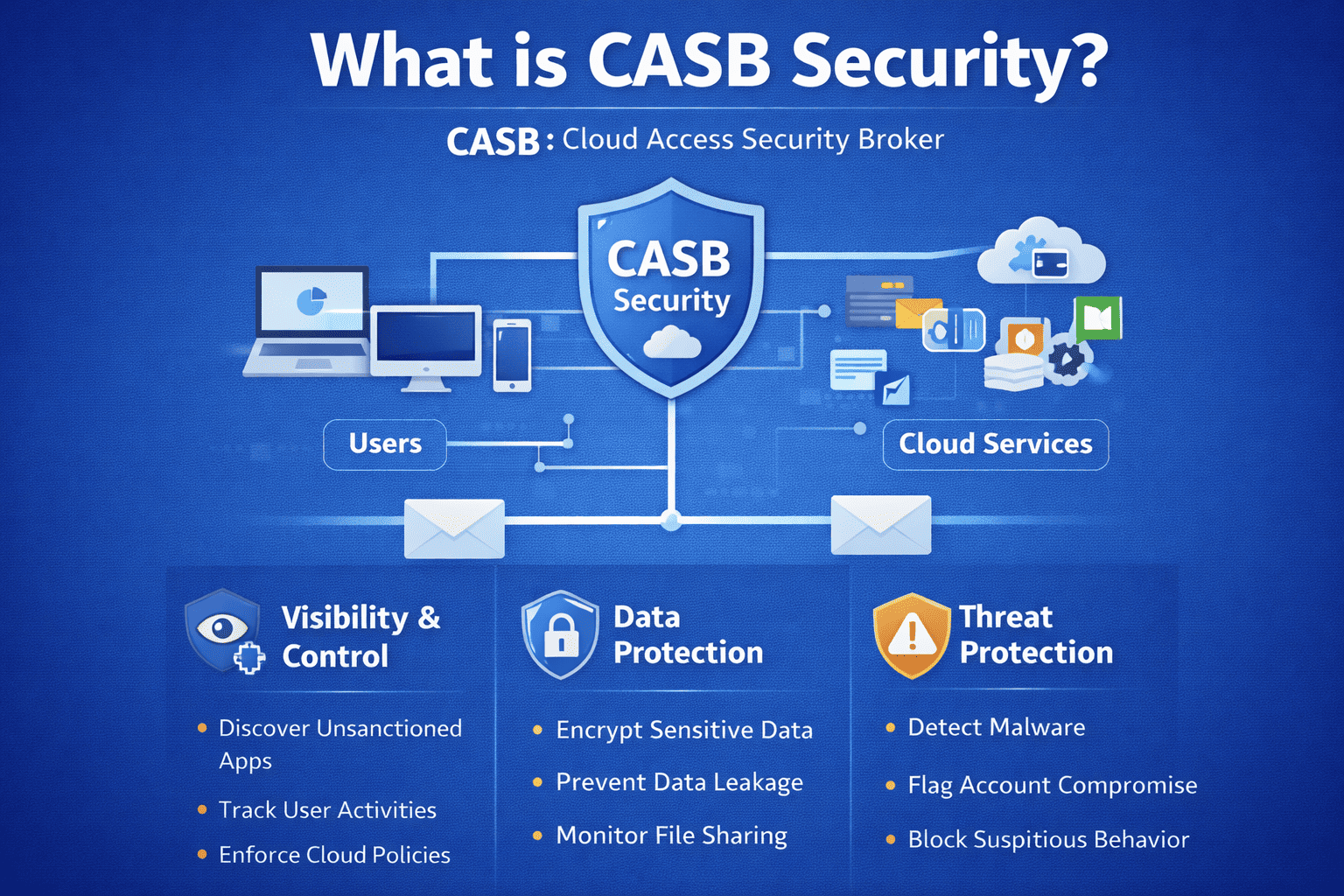
A Cloud Access Security Broker (CASB) acts as a gatekeeper between users and cloud applications, providing visibility, control, and threat protection. For IT managers and cybersecurity leaders, CASB security bridges the gap between on-premises policies and cloud services.
In this guide, we’ll explore what CASB security is, how it works, core capabilities, business benefits, use cases, risks, and how organizations can implement it effectively.
What Is CASB Security?
CASB security refers to the use of a Cloud Access Security Broker to monitor and control data and user activity across cloud applications.
A CASB sits between:
Cloud service users
SaaS applications
Enterprise policies
It enforces security policies for cloud environments while providing visibility into data movement and user behavior.
In simple terms, CASB security ensures that cloud usage aligns with organizational security standards.
Why CASB Security Is Critical Today
Cloud usage is growing rapidly.
Organizations now rely on:
Microsoft 365
Google Workspace
Salesforce
AWS
Azure
Hundreds of SaaS applications
Without CASB security, businesses lack visibility into how cloud services are being used—and misused.
Key risks without CASB security:
Shadow IT expansion
Data leakage
Unauthorized access
Compliance violations
Insider threats
CASB security addresses these risks directly.
How CASB Security Works
To fully understand CASB security, it helps to examine how it operates.
A CASB can function in several modes:
1. API-Based Integration
Connects directly to cloud services through APIs.
Monitors stored data
Detects misconfigurations
Scans for sensitive information
2. Proxy-Based Deployment
Intercepts traffic between users and cloud apps.
Real-time policy enforcement
Inline data loss prevention
Immediate threat blocking
3. Hybrid Deployment
Combines API and proxy capabilities for comprehensive coverage.
Most enterprise CASB security implementations use hybrid approaches.
Core Capabilities of CASB Security
CASB security solutions typically focus on four pillars.
1. Visibility
Visibility is the foundation of cloud security.
CASB security helps organizations:
Discover all cloud applications in use
Identify shadow IT
Monitor user behavior
Track sensitive data movement
You cannot secure what you cannot see.
2. Data Security
Protecting sensitive information is critical.
CASB security provides:
Data Loss Prevention (DLP)
Encryption enforcement
Tokenization
Access controls
This prevents accidental or malicious data exposure.
3. Threat Protection
Cloud environments are frequent targets.
CASB security detects:
Account compromise
Malware uploads
Suspicious login behavior
Unusual data transfers
Threat detection is behavior-driven and policy-based.
4. Compliance
Regulatory compliance is complex in cloud environments.
CASB security supports:
GDPR
HIPAA
PCI DSS
SOC 2
ISO standards
It helps maintain audit trails and enforce governance policies.
CASB Security vs Traditional Firewalls
Traditional firewalls protect network perimeters. CASB security protects cloud interactions.
| Feature | Firewall | CASB Security |
|---|---|---|
| Cloud visibility | Limited | Comprehensive |
| SaaS control | Minimal | Granular |
| Data monitoring | Network-level | Application-level |
| Remote workforce | Limited | Strong |
Modern environments require both.
CASB Security and Shadow IT
Shadow IT is a major concern.
Employees often use:
File-sharing platforms
Messaging tools
Collaboration apps
Personal cloud storage
CASB security identifies and assesses these applications.
It can:
Block risky apps
Rate application risk levels
Enforce policies automatically
This reduces unmanaged exposure.
CASB Security in Remote Work Environments
Remote and hybrid work has expanded the attack surface.
CASB security protects:
Remote endpoints
Cloud logins
SaaS interactions
Mobile access
Location-based risk policies enhance protection.
CASB Security and Zero Trust
Zero Trust models require continuous verification.
CASB security supports Zero Trust by:
Validating identity continuously
Monitoring user behavior
Enforcing least-privilege access
Blocking risky sessions
It strengthens identity-driven security.
Common CASB Security Use Cases
CASB security supports multiple operational scenarios.
Common use cases include:
Monitoring cloud storage for sensitive data
Blocking uploads of confidential files
Detecting compromised user accounts
Preventing data sharing outside the organization
Enforcing regional data policies
These use cases improve risk management.
CASB Security for Different Industries
Different industries face unique cloud security challenges.
Healthcare
Protect patient records and meet HIPAA requirements.
Financial Services
Prevent fraud, data exfiltration, and insider misuse.
Retail and E-Commerce
Secure customer payment information.
Technology and SaaS
Protect intellectual property and development environments.
Government
Enforce strict access and compliance standards.
CASB security adapts to industry-specific needs.
Benefits of CASB Security
Organizations implementing CASB security often experience:
Greater cloud visibility
Reduced data leakage
Stronger compliance posture
Improved incident response
Better risk scoring
For executives, this translates to reduced cyber risk.
Limitations of CASB Security
CASB security is powerful—but not complete.
It does not:
Replace endpoint security
Stop all phishing attacks
Protect on-premises systems
Eliminate need for backups
It must be part of a layered security strategy.
CASB Security vs Secure Access Service Edge (SASE)
SASE combines networking and security into a unified framework.
CASB is often a core component of SASE.
SASE includes:
CASB
Secure Web Gateway (SWG)
Zero Trust Network Access (ZTNA)
Firewall-as-a-Service
CASB security plays a foundational role in cloud-focused SASE models.
CASB Security Implementation Best Practices
Implementing CASB security requires planning.
Recommended steps:
Identify all cloud applications
Assess risk levels
Define cloud usage policies
Deploy in monitoring mode first
Gradually enforce policies
A phased approach minimizes disruption.
Common CASB Deployment Challenges
Organizations may encounter:
Resistance from business units
Complexity in policy configuration
Integration issues
Alert fatigue
Proper governance and stakeholder buy-in are critical.
Future of CASB Security
Cloud adoption will continue expanding.
Emerging trends include:
AI-powered anomaly detection
Automated policy enforcement
Integration with Extended Detection and Response (XDR)
Deeper behavioral analytics
CASB security is evolving toward proactive, intelligent cloud defense.
FAQs: CASB Security
1. What is CASB security?
CASB security is a cloud security solution that monitors and controls access to cloud applications.
2. Why is CASB important?
It provides visibility, data protection, threat detection, and compliance enforcement for cloud usage.
3. Does CASB replace firewalls?
No. It complements traditional network security tools.
4. Is CASB only for large enterprises?
No. SMBs also benefit from cloud visibility and control.
5. Can CASB stop insider threats?
It can detect risky behavior and enforce data access policies.
Final Thoughts: Why CASB Security Matters
Cloud transformation has reshaped modern business. But increased cloud usage demands stronger oversight. CASB security fills the visibility and control gap between users and cloud services.
For IT managers, it reduces blind spots.
For cybersecurity teams, it enhances monitoring.
For executives, it lowers enterprise risk.
CASB security is no longer optional—it is a foundational component of modern cloud protection.
Take the Next Step Toward Stronger Cloud Protection
Ready to gain deeper visibility and control over your cloud environments?
👉 Register today:
https://openedr.platform.xcitium.com/register/
Discover how advanced cloud and endpoint security solutions help organizations secure SaaS applications, prevent data leakage, and stay ahead of modern cyber threats.