What Difference Does Best EDR (EndPoint Detection And Response) Service Make To Start-ups?
Updated on July 24, 2023, by OpenEDR

Have you ever wondered, what will happen to your business or brand if it is violated by the unauthorised source(s)? What damage can it cause to your reputation and brand’s budding image? With the advancement of
technology and its misuse, any uprising brand should be well prepared to handle the situation easily and comfortably. To attain impeccable cyber threat detection services, every brand needs the assistance of the
best EDR service provider.
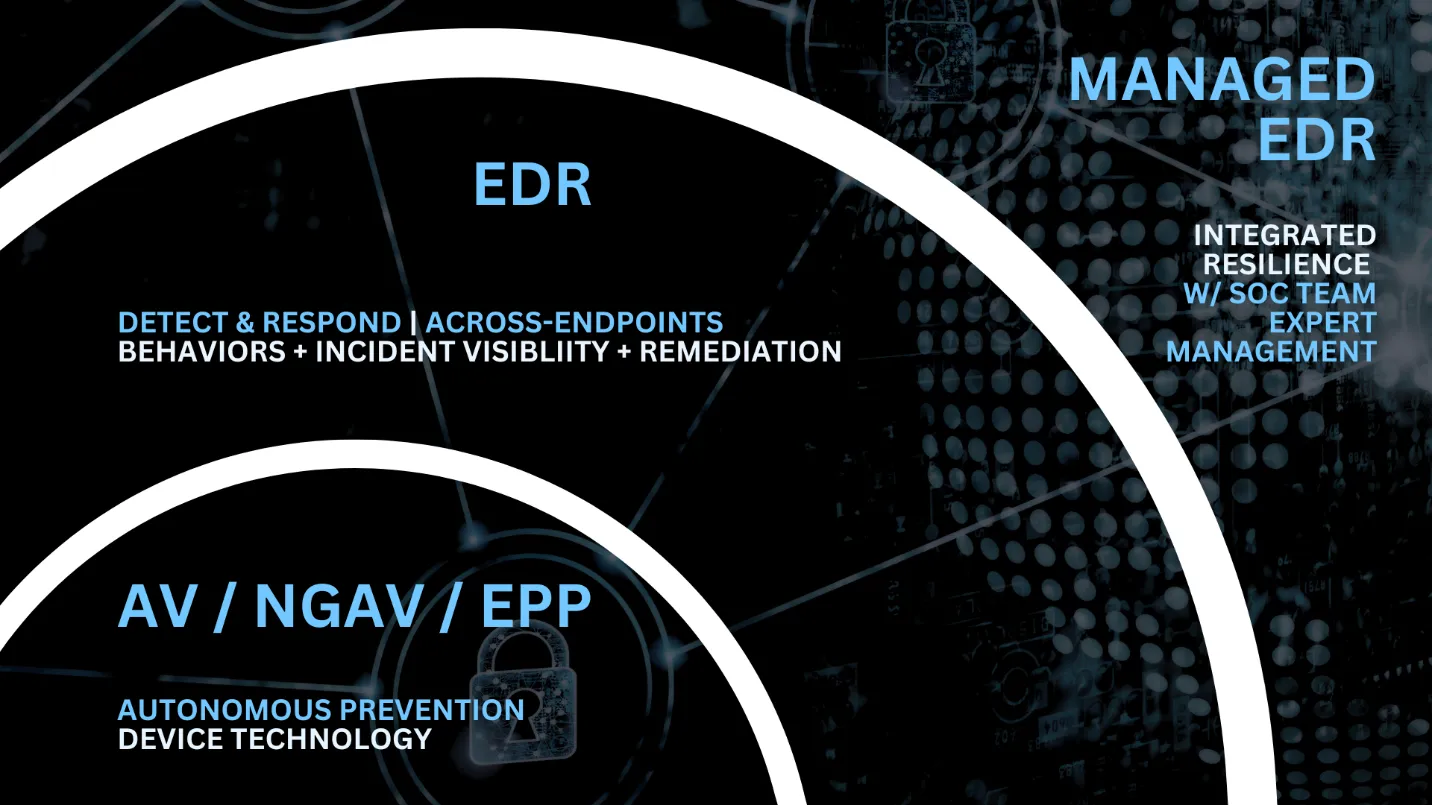
The best EDR or Endpoint Detection and Response service
providers are responsible for protecting the vitality of start-up businesses by effectively detecting, analyzing, and
responding to security incidents at the endpoint level. Additionally, the best EDR services provider aims at
various adjoining factors.
Benefits of hiring the best EDR service provider
Endpoint Detection and Response service helps the business by making them aware and prepared for the uprising threat at
the endpoint. The best EDR service providers are well aware of the challenges that may arise with the uprising and
budding businesses. To tackle them with ease and efficiency, they make several result-oriented offers. There are several
benefits of hiring the best EDR team. Let’s discuss a few of them.
Early Threat Detection: The most reliable and best EDR system efficiently detects the potential threat at
the endpoint level. It utilizes various techniques such as behavior analysis, machine learning as well as threat
intelligence. Their operations are completely different fron the ones deployed in the traditional solution.
The best EDR system is capable of detecting both known and unknown threats and thus reduces the risk of attack
going to occur.
Rapid Incident Response: Endpoint
detection and response is well known for its real- visibility into the endpoint activities. This
aspect of the best EDR system allows the security team to respond effectively to security incidents.
Additionally, the EDR solutions enable security workers to contain and remediate problems quickly by giving complete
information about the attack, compromised endpoints, and attack pathways.
Proactive Threat Hunting: The best EDR service provider is renowned for motivating start-up owners to
actively search for
potential and hazardous cyber threats within the endpoint environment network. The security team members may use the
capabilities of the EDR system to analyze endpoint telemetry data, detect anomalies, and identify indicators of
compromise (IOCs). With the advanced hunting for the threats, the start-ups can stay a step ahead of the attackers
before they can cause harm to the business.
Improvised Investigation: The Best EDR service providers Assist the investigation team with the thorough
inspection procedure.
The service provider valuable insight into the main cause of the attack, the extent of the compromise, and any
lateral movement within the network. The detailed information provided by the best EDR service providers helps
the investigating team to find the root cause of the cyber attack
and take the appropriate action to prevent future occurrences.
Compliance and Regulatory Requirements: The best EDR service provider system helps start-ups to meet
compliance requirements by making the
availability of detailed logs and audit trials of endpoint activities. The detailed logs presented by the service
provider can turn out to be invaluable during forensic investigations, incident reporting, and demonstrating
adherence to industry-specific regulations. The best EDR systems
promote a robust security posture for the business, which is efficiently essential for the maintenance and
preservation of the data and confidentiality of the business.
Enhanced Endpoint Visibility and Control: The best EDR systems offer businesses comprehensive visibility
into endpoint activities, including
software installations, patch levels, user behavior, and system configurations. This visibility enables start-ups to
enforce security policies, identify violations, and promptly address vulnerabilities.
The best EDRsystems also allow organizations to remotely isolate or remediate compromised
endpoints, limiting the spread of attacks.
What are the common types of Cyber Attacks?
In the world of cybercrime, every day, there is a
new addition to the variation of cyber attacks. However, over the recent studies conducted there by technical
professionals, few enlisted cyber-attacks are primarily prevalent. Fortunately, the best
EDR service providers efficiently handle these cyber attacks with the help of
skilled technicians.
- Malware
- Phishing
- IoT-Based Attacks
- Spoofing
- Denial-of-Service (DoS) Attacks
- Identity-Based Attacks
- Code Injection Attacks
- Supply Chain Attacks
Intangible benefits of hiring the best EDR service provider.
Apart from the above-mentioned benefits, there are other benefits of impeccable services
from the best EDR service providers. Like,
- Endpoint Detection and Response
service provider protects the confidential information of the Startup businesses. - The best EDR service provider safeguards the surviving
provider’s goodwill and protects their
reputation. - It is extremely important to protect
the start-ups from heavy loss and financial indebt. - It protects the various system(s) from being the target of the next
attack.
Conclusion – Best EDR
It is obvious that every startup essentially needs the best EDR system to preserve its integrity
and support its proper operation. The effective and efficient service provider helps start-ups to safeguard themselves
from the invasion of unwanted and malicious attacks. Additionally, it helps the start from losing their confidential and
important file, which eventually protects its reputation and goodwill. Furthermore, it ensures that the organization
runs smoothly.
OpenEDR® is the one-stop open source EDR solutions provider for giving start-ups the best EDR system. Our
efficient team is skilled in providing our clients with ongoing monitoring, spotting loopholes, pinpointing the
problem’s origin, and launching the best solutions. With the aid of the greatest technology, which offers defense
against technologically malicious acts, we secure the organization’s safety.